Data race
Multiple tasks perform unprotected nonatomic operations on shared variable
Description
This checker is deactivated in a default Polyspace® as You Code™ analysis. See Checkers Deactivated in Polyspace as You Code Analysis (Polyspace as You Code).
This defect occurs when:
Multiple tasks perform unprotected operations on a shared variable.
At least one task performs a write operation.
At least one operation is nonatomic. To detect data race on both atomic and nonatomic operations, use the options
-detect-atomic-data-race. See Extend Data Race Checkers to Atomic Operations.
The defect checker reports one data race result for each shared variable with conflicting read/write or write-write operations. For each result, you see a list of conflicting accesses in the event list. The list of conflicting accesses is representative and not exhaustive.
If you activate this checker without specifying the multitasking options first, you see a warning in the log:
Warning: Checker 'Data Race' is activated but no protection have been defined
To find this defect, specify your tasks and protections for shared variables using one of these methods:
Invoke one of the concurrency primitives that Polyspace Bug Finder™ can detect automatically. See Auto-Detection of Thread Creation and Critical Section in Polyspace.
Specify tasks and protections for shared variables explicitly before analysis as configuration options. See Configure Multitasking Checks.
If your code contains a defect such as Double lock that prevents execution of subsequent code, Polyspace does not report possible data races in the subsequent code.
Risk
Data race can result in unpredictable values of the shared variable because you do not control the order of the operations in different tasks.
Data races between two write operations are more serious than data races between a write and read operation. Two write operations can interfere with each other and result in indeterminate values. To identify write-write conflicts, use the filters on the Detail column of the Results List pane. For these conflicts, the Detail column shows the additional line:
Variable value may be altered by write-write concurrent access.
Fix
To fix this defect, protect the operations on the shared variable using critical sections, temporal exclusion or another means. See Protections for Shared Variables in Multitasking Code.
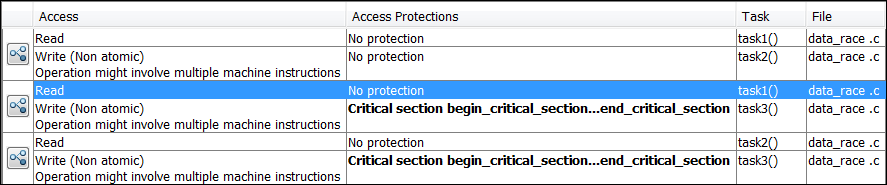
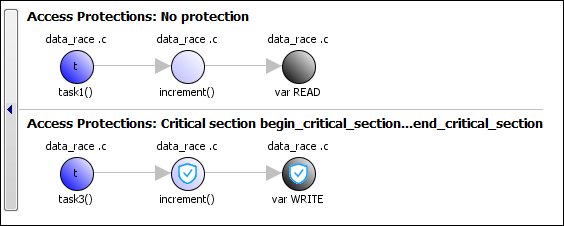
To identify existing protections that you can reuse, see the table and graphs associated with the result. The table shows each pair of conflicting calls. The Access Protections column shows existing protections on the calls. To see the function call sequence leading to the conflicts, click the ![]() icon. For an example, see below.
icon. For an example, see below.
Extend Checker
Extend this checker to check for data races in operations that Bug Finder might not detect by default. For instance:
You might be using multithreading functions that are not supported by Polyspace. Extend this checker by mapping the functions of your multithreading functions to their known POSIX® equivalent. See Extend Concurrency Defect Checkers to Unsupported Multithreading Environments.
Polyspace assumes that certain operations are atomic and excludes them from data race checks. See Define Atomic Operations in Multitasking Code. These assumptions might not apply to your environment. To extend the data race checkers to include these operations, use the option
-detect-atomic-data-race. See Extend Data Race Checkers to Atomic Operations.
Note that the checker reports one data race result per shared variable. The event list for the result shows a limited number of conflicting read/write and write-write conflicts. You cannot customize these limits.
Examples
Result Information
| Group: Concurrency |
| Language: C | C++ |
| Default: On |
Command-Line Syntax:
DATA_RACE
|
| Impact: High |
PQL Name:
std.defects.DATA_RACE
|
Version History
Introduced in R2014b
See Also
Disabling all interrupts (-routine-disable-interrupts -routine-enable-interrupts) | Temporally exclusive tasks (-temporal-exclusions-file) | Critical section details (-critical-section-begin -critical-section-end) | Tasks (-entry-points) | Configure multitasking manually | Target processor type (-target) | Find defects (-checkers) | Data race through standard library function call | Deadlock | Destruction of locked mutex | Double lock | Double unlock | Missing lock | Missing unlock
Topics
- Analyze Multitasking Programs in Polyspace
- Protections for Shared Variables in Multitasking Code
- Interpret Polyspace Bug Finder Results in Polyspace Platform User Interface
- Interpret Bug Finder Results in Polyspace Access Web Interface (Polyspace Access)
- Address Polyspace Results Through Bug Fixes or Justifications
- Address Results in Polyspace Access Through Bug Fixes or Justifications (Polyspace Access)
- Define Atomic Operations in Multitasking Code
- Extend Concurrency Defect Checkers to Unsupported Multithreading Environments
- Extend Data Race Checkers to Atomic Operations